The image is built, scanned, and pushed. The version tag is v0.1.0-alpha.7.
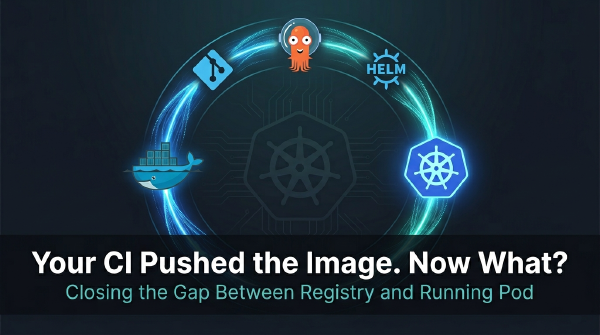
The artifact is already hardened. From FinTech to Homelab: Writing an Enterprise-Ready Dockerfile for Hugo was about building the container correctly. This post is about everything that has to happen after that.
In the previous post, I laid out my plan: treat this blog as a production application and host it using the same standards I apply when architecting platforms for private banking and fintech.
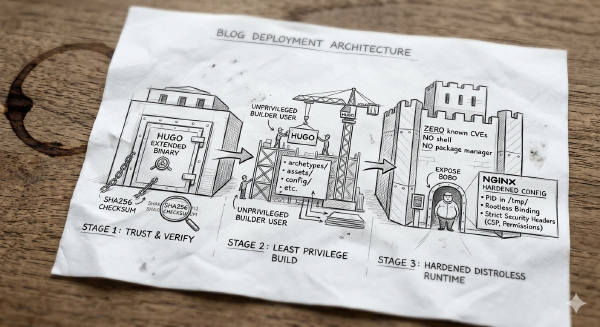
The Enterprise Traceability Problem # Guessing whether v1.3.0 in production actually includes yesterday’s critical security patch is a dangerous game. Knowing exactly which version of an artifact is running in any given environment isn’t just a nice-to-have dashboard feature… it’s the foundation of a reliable release process. You can never afford to wonder if the build candidate QA just signed off on is truly the exact same binary you are deploying to users.
The Question That Changed Everything # Over the past months, I’ve received a variation of the same question more than any other:
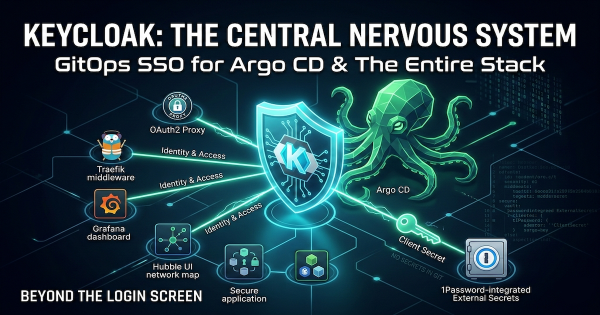
More Than Just a Login Screen # In our last post, we deployed a production-ready Keycloak cluster. But an Identity Provider (IdP) in isolation is just a database of users. Its true power lies in being the architectural enforcement point for your entire platform.
Take Back Control of Your Identity # Over the last few months, we’ve built a platform that rivals small enterprise setups. We have established a resilient networking layer with automated TLS, deployed distributed block storage with Longhorn, and mastered PostgreSQL on Kubernetes with CloudNativePG.
The “Stateful” Reality Check # In our last post, we solved the persistence layer by deploying Longhorn on Talos Linux. We finally have a place to put data. But a raw block device isn’t a database.
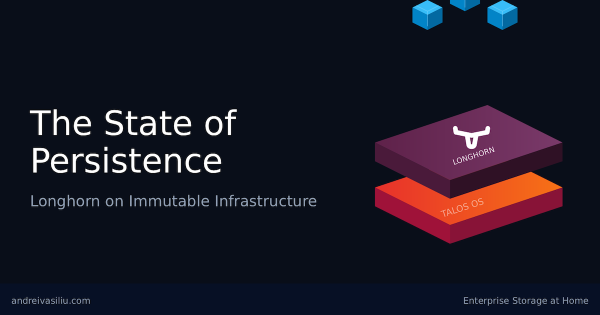
The Paradox of Statelessness # Kubernetes is designed to be ephemeral. Pods die, nodes are replaced, and the cluster heals itself. This “stateless” philosophy is efficient for application logic, but it hits a hard wall when you need to store data. Databases, message queues, and media servers all need a place to live that persists beyond a pod restart.
Locking it Down - From HTTP to HTTPS # In the preceding chapters, we established the networking foundation for a production-grade bare-metal Kubernetes platform.